Laws and regulations governing cybersecurity
5. Information Security Management System
5.2. Risk management
According to Article According to Article 7 of the NIS, each Member State is to adopt a national strategy for network and information systems security, setting out strategic objectives and relevant policy and regulatory measures to achieve and maintain a high level of network and information systems security. The subject of the national strategy for the security of networks and information systems includes mainly the following objectives and measures:
|
a) |
the objectives and priorities of the national strategy for network and information security; |
|
b) |
the administrative framework for meeting the objectives and priorities of the national strategy for the security of networks and information systems, including the role and responsibilities of governments and other relevant entities; |
|
c) |
identification of preparedness, response and recovery measures, including public-private cooperation; |
|
d) |
definition of education, information and training programs related to the national strategy for the security of networks and information systems; |
|
e) |
definition of research and development plans related to the national strategy for network and information systems security; |
|
f) |
risk assessment plan for risk identification; |
|
g) |
a list of the various entities involved in the implementation of the national strategy for network and information systems security. |
According to Czech legislation, risk assessment means the overall process of risk identification, analysis and evaluation.
The risk assessment process is addressed, for example, by ISO/IEC 27005, where this process is demonstrated.
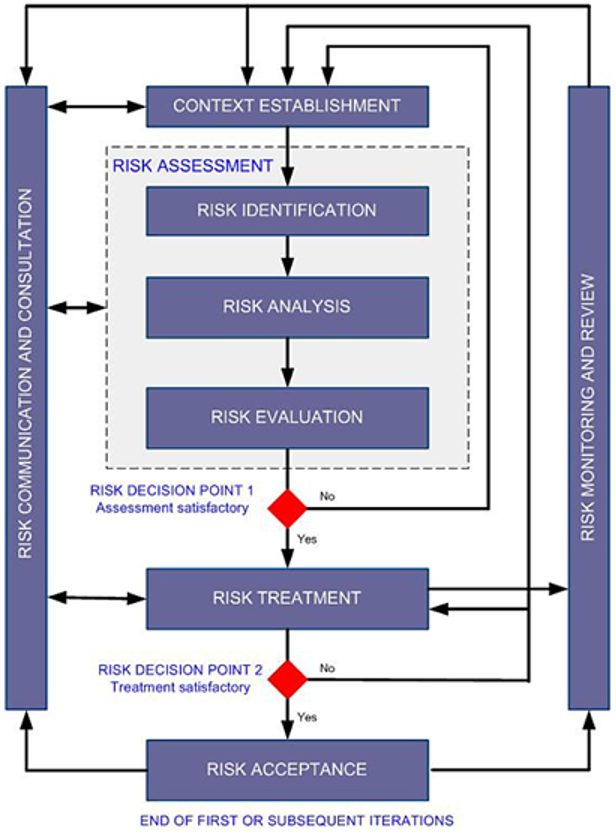
Figure: Demonstration of risk assessment in ISMS[1]
The PDCA model must also be respected in the risk assessment process, but it is adapted for risk assessment.[2]
|
ISMS process |
Risk assessment process in ISMS |
|
Plan |
Creating a context Risk assessment Development of a risk management plan Risk acceptance |
|
Do |
Implementation of the risk management plan |
|
Check |
Continuous monitoring and review of risks |
|
Act |
Maintaining and improving the risk assessment and management process Management process |
As for the risk management itself, it is possible to graphically illustrate this process as follows:

Figure: Risk management in the ISMS process[3]
|
ISMS Plan |
ISMS Plan |
|
Rozsah ISMS |
ISMS scope |
|
Politika ISMS |
ISMS policy |
|
Přenesení rizika |
Risk transfer |
|
Katalog opatření ISO/IEC 27002:2005 |
Catalogue of measures ISO/IEC 27002:2005 |
|
Odůvodnění výběru opatření ISMS |
Justification for the choice of ISMS measures |
|
Souhlas vedení se zavedením ISMS a se zbytkovými riziky |
Management’s approval of ISMS implementation and residual risks |
|
Prohlášení a aplikovatelnosti |
Declaration and applicability |
|
Důvody pro neaplikování |
Reasons for not applying |
|
Neaplikovaná opatření ISMS |
Unapplied ISMS measures |
|
Metoda hodnocení rizik |
Risk assessment method |
|
Aktiva ISMS |
ISMS assets |
|
Garant aktiva |
Asset guarantor |
|
Typy aktiv - informační, HW, SW, služba, lidé, ...
|
Types of assets - information, HW, SW, service, people, ...
|
|
Ohodnocení aktiva - důvěrnost, integrita, dostupnost |
Asset valuation - confidentiality, integrity, availability |
|
Skupiny aktiv ISMS |
ISMS asset groups |
|
Vyhnutí se riziku |
Risk avoidance |
|
Rozsah dopadů a škod - ohrožení funkčnosti, právní dopady |
Extent of impacts and damages - endangerment of functionality, legal consequences |
|
Hrozba - pravděpodobnost vzniku škody |
Threat - probability of damage |
|
Zranitelnost - pravděpodobnost selhání opatření |
Vulnerability - probability of failure of a measure |
|
Rizika ISMS |
ISMS risks |
|
Aplikování opatření ISMS |
Application of ISMS measures |
|
Akceptování rizika |
Risk acceptance |
|
Opatření ISMS |
ISMS measures |
|
Vliv na zranitelnost |
Impact on vulnerability |
|
Zbytková rizika ISMS |
Residual ISMS risks |
|
ISMS Do |
ISMS Do |
|
Plán zvládání rizik |
Risk management plan |
The value of risk is most often expressed as a function affected by impact, threat and vulnerability. For example, the following function can be used for self-assessment of risk:
Risk = impact * threat * vulnerability
If an obligor uses a risk assessment method that does not differentiate between threat and vulnerability assessments, the threat and vulnerability assessment scales may be combined. The merging of scales should not lead to a loss of the ability to distinguish between levels of threat and vulnerability. For this purpose, for example, a comment can be used that clearly expresses both the level of threat and the level of vulnerability. The same applies in cases where the obligor uses a different number of levels to assess impacts, threats, vulnerabilities and risks.[4]
Appendix 3 to the CSD further lists the scales used to assess threats, vulnerabilities and risks.
|
Level |
Description |
|
Low |
Threat does not exist or is unlikely. The expected threat attempt is not more frequent than once every 5 years. |
|
Medium |
Threat is unlikely to likely. The expected threat attempt is in the range from 1 year to 5 years. |
|
High |
Threat is likely to very likely. The expected threat attempt is in the range from 1 month to 1 year. |
|
Critical |
Threat is very likely or more or less certain. The expected threat attempt is more frequent than once a month. |
Figure: Threat assessment scale
|
Level |
Description |
|
Low |
Vulnerability does not exist or is unlikely to be exploited. Security measures are in place that are able to detect possible vulnerabilities or possible attempts to exploit them in a timely manner. |
|
Medium |
Vulnerability exploitation is
unlikely to likely. |
|
High |
Vulnerability exploitation is likely to very likely. Security measures are in place, but their effectiveness does not cover all the necessary aspects and is not regularly checked. There have been some partial successful attempts to overcome security measures. |
|
Critical |
Vulnerability
exploitation is very likely or more or less certain. |
Figure: Vulnerability assessment scale
|
Level |
Description |
|
Low |
Risk is considered acceptable. |
|
Medium |
Risk can be reduced by less demanding measures or in case of higher intensity of measures the risk is acceptable. |
|
High |
Risk is unacceptable in the long run, and systematic steps must be taken to eliminate it. |
|
Critical |
Risk is unacceptable, and steps must be taken to eliminate it immediately. |
Figure: Scale for risk assessment
[1] ISO/IEC 27005 p. 8
[2] ISO/IEC 27005 p. 9
[3] POŽÁR, Josef and Luděk NOVÁK. Pracovní příručka bezpečnostního manažera. Prague: AFCEA, 2011. ISBN 978-80-7251-364-2, p. 12, or: POŽÁR, Josef and Luděk NOVÁK. Systém řízení informační bezpečnosti. [online]. [cit. 06/07/2018]. Available from: https://www.cybersecurity.cz/data/srib.pdf p. 5
[4] See Appendix 3 (5) to the CSD (Cybersecurity Decree)
